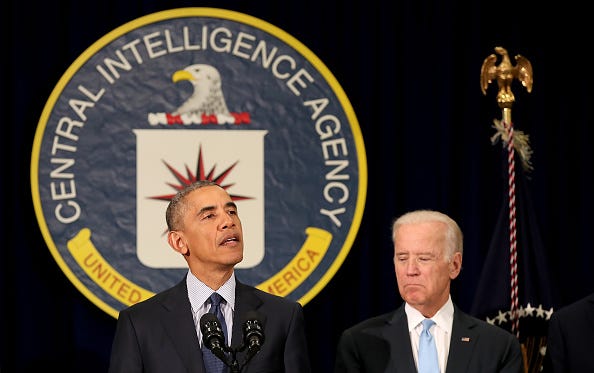
Who burnt the CIA's assets in China?
From 2010 to 2012, the CIA suffered its worst losses in China as the Ministry of State Security went about dismantling spy networks with unerring precision

After the Tiananmen unrest and collapse of communist governments in Europe, the domestic security apparatus underwent rapid expansion. A massive number of formal and informal agents of the state were recruited for counterintelligence. Ever since, China has been considered a notoriously problematic country for foreign spy agencies to penetrate.
Despite the challenges, the CIA found a way through, and in 2010, it hit a purple patch. Painstakingly built over the years, its network of sources deep inside the Chinese bureaucracy was relaying the sort of sensitive information about the inner workings of the Chinese government that, until a few years ago, would have seemed impossible to access.
Towards the end of the year, though, the flow of information petered out. Soon afterwards, the CIA’s sources began disappearing. With alarm bells ringing in Langley, hundreds of counterintelligence officials at the CIA and the FBI formed a joint investigation team.
There is a mole…
Opinions were divided. A few were convinced that the CIA had a mole a la Aldrich Ames, who is serving a life sentence without parole for spying for the Soviet Union.
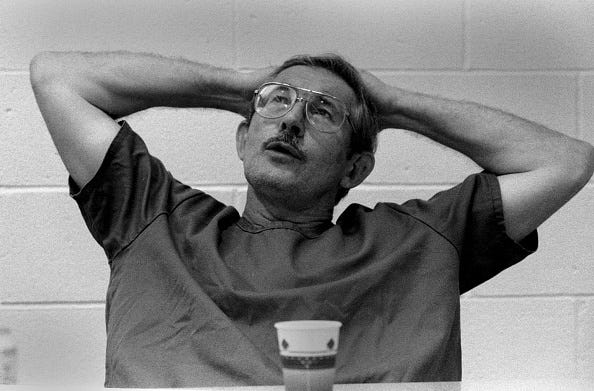
The mole hunt finally zeroed in on a former CIA officer who had worked in the agency’s division tasked with operations in China. Of Chinese descent, the officer had moved to Hong Kong after parting ways with the CIA. The sources had begun disappearing a short while after his departure. But the agency didn’t have enough evidence to arrest him.
There was a second group among the investigators who believed sloppy tradecraft by handlers was to blame. In the decade since the September 11th attacks, the CIA had reoriented itself for counterterrorism. And some believed that this reorientation had resulted in the agency’s bread-and-butter of spycraft becoming rusty.
Some officers met their sources at a restaurant where Chinese agents had planted listening devices, former officials said, and even the waiters worked for Chinese intelligence.
—Mazzetti et al, New York Times

In the meantime, the Chinese continued to identify and neutralise CIA assets well into 2012, when the CIA lured the former operative back to the United States. During an interview, he justified staying back in Asia with his family, and returned to Hong Kong.
But there was a third group among the investigators who felt that the answer was to be found online. Handlers in the CIA were using a hidden communications app on publicly accessible websites to communicate with their sources in hostile countries, including China. And some believed this system had been compromised.
The Chinese weren’t the first

China wasn’t even the first adversary to compromise the CIA. In 2009, after the Obama administration announced the discovery of a secret Iranian enrichment facility, the Iranian Ministry of Intelligence (VAJA) began a mole hunt to identify the source. By 2010, Iran had tasted success, identifying CIA assets. In 2011, VAJA dismantled a CIA network in Iran. Some assets were executed, others were imprisoned. A few were successfully extracted by the CIA.

In May 2011, Iranian intelligence officials announced publicly that they had broken up a ring of 30 CIA spies; U.S. officials later confirmed the breach to ABC News, which also reported on a potential compromise to the communications system.
—Zach Dorfman and Jenna McLaughlin, Yahoo News.
Whether the Iranians cracked the communications system first, or if a double agent led them to it remains an unanswered question. US officials hint at the latter.
…two former U.S. intelligence officials said that the Iranians cultivated a double agent who led them to the secret CIA communications system.
—Zach Dorfman and Jenna McLaughlin, Yahoo News.
Once they knew what they were looking for, it wouldn’t have been too difficult for them to use the communications system itself to identify other CIA assets in their country. And that’s exactly what appears to have happened.
Israeli intelligence warned the CIA that a few of their assets had been compromised by the Iranians. But by then, the Iranians had compromised the communications system itself.
After they had figured out what sort of websites they were looking for, the Iranians reportedly used Google’s search engine to find other websites that matched the pattern. Then they tracked people who were visiting those websites from Iran, and began dismantling the CIA’s network.
Right around the time Iran was dismantling that CIA network, the Chinese had apprehended and executed roughly 30 CIA assets. But the CIA had their man. They insisted, officially, that the network had been blown by a former CIA employee named Jerry Chun Shing Lee.

Beginning sometime in May 2010 and continuing into at least 2011, Lee received requests for information, or taskings, from the Chinese Intelligence Officers (IOs)…[A search in 2012 of Lee’s hotel room in Honolulu] revealed that Lee possessed a day planner and an address book that contained handwritten notes [including] among other things, intelligence provided by CIA assets, true names of assets, operational meeting locations and phone numbers, and information about covert facilities.
—US Dept of Justice
Jerry Lee was sentenced to 19 years in prison. But intelligence officials maintain — off the record — that Lee’s purported betrayal could not have resulted in the rapid and extensive damage inflicted on CIA’s networks in China. And it doesn’t explain the damage done to CIA’s operations in Iran at all. Jerry Lee did not have access to information about CIA assets in that geography.
It isn’t clear exactly when it dawned upon the CIA, but there were two frightening aspects to the communication system breach that they now had to grapple with.
Right around the time China and Iran scored their respective counterintelligence coups, the intelligence services of the two countries met with their counterparts in Russia to discuss “cyber issues”. And US officials believe the Chinese shared their penetration of the CIA’s system with their Russian counterparts.
As if this wasn’t worrying enough, the CIA also realised that if these countries could identify assets in their respective countries using these techniques, they could also identify CIA assets in other countries.
Former officials said the fallout from the compromises was likely global in scope — potentially endangering all CIA sources that used some version of this internet-based system worldwide.
—Zach Dorfman and Jenna McLaughlin, Yahoo News.
And it could have been prevented
In the early 2000s, a CIA contractor named John Reidy was tasked with identifying human intelligence targets for recruitment. To enable him to perform his job, he was given access to a CIA system used to communicate with potential assets. Around 2006, he noticed several anomalies and conflicting intelligence that suggested that their operations were compromised.
When many assets ceased communication, his boss tasked him with identifying what had gone wrong and evolving countermeasures. Reidy and his boss then took their analysis and recommendations upstairs. Things were desperate. In Reidy’s words:
I provided at least 25 recommendations that we impose immediately to mitigate the total collapse of our [redacted] intelligence collection efforts.
But his department’s funds were contingent on results, and the higher ups were unwilling to do anything to stop the gravy train. So his analysis and recommendations were buried in secret files, and a few months later Reidy was shunted to a different role. Shortly after that, they declined to renew his contract.
Meanwhile throughout 2010, I started to hear about catastrophic intelligence failures…More than one government employee reached out to me and notified me that the “nightmare scenario” I had described and tried to prevent had transpired. I was told that upwards of 70% of our operations had been compromised
Jerry Lee couldn’t have compromised all that, and he certainly couldn’t have compromised the CIA’s Iranian networks.
Based on media reports about the CIA’s communication system, The Citizen Lab from the University of Toronto conducted an independent investigation. Their findings align with the whistleblower complaint filed by Reidy.
The websites, which purported to be news, weather, sports, healthcare, and other legitimate websites, appeared to be localized to at least 29 languages and geared towards at least 36 countries…The bulk of the websites that we discovered were active at various periods between 2004 and 2013.
—The Citizen Lab, University of Toronto
The Citizen Lab identified 885 websites used by the CIA.
Can you imagine how different this whole story would’ve turned out if the CIA [inspector general] had acted on Reidy’s warnings instead of going after him? Can you imagine how different this whole story would’ve turned out if the congressional oversight committees had done oversight instead of taking CIA’s word that he was just a troublemaker?
—Kel McClanahan, Reidy’s attorney in the Yahoo report
A national security analyst with the Government Accountability Project put it in starker terms:
This is one of the most catastrophic intelligence failures since Sept. 11. And the CIA punished the person who brought the problem to light.
—Irvin McCullough, as quoted in the Yahoo report.
Have you read my spy novels? The Let Bhutto Eat Grass series deals with nuclear weapons espionage in India, Pakistan, and Europe during the Cold War.
Further reading
The CIA's communications suffered a catastrophic compromise. It started in Iran — Yahoo News
Pentagon, CIA instructed to re-investigate whistleblower cases
John Reidy’s whistleblower complaint to the Inspector General of the Intelligence Community (PDF link)
Statement on the fatal flaws found in a defunct CIA covert communications system — Citizen Lab
Killing C.I.A. Informants, China Crippled U.S. Spying Operations — NYT





